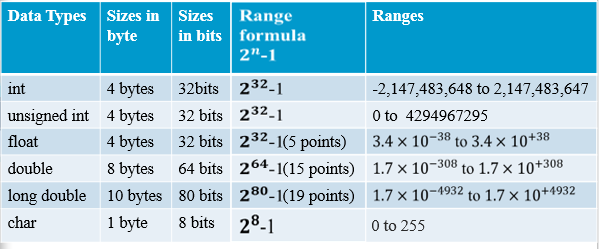
Somewhere in a production pricing engine, a 32-bit integer silently wraps around during a notional accumulation, a Greeks ladder miscounts its buckets, or a risk aggregation quietly produces a number that is just slightly wrong — and nobody notices until the end-of-day reconciliation, or worse, until a trader calls. Arithmetic overflow is one of the oldest bugs in systems programming, yet in C++ it carries a particularly sharp edge: signed overflow is undefined behaviour, meaning the compiler is not only permitted to produce a wrong answer, it is permitted to optimise away the very branch you wrote to catch it. In latency-sensitive financial code, where you’re burning through millions of option valuations or margin calculations per second, this is not a theoretical concern.
The good news is that modern C++ — and GCC/Clang long before the standard caught up — gives you a near-zero-cost escape hatch: __builtin_add_overflow, __builtin_mul_overflow, and their family members. These compiler intrinsics lower directly to native overflow-checking instructions (think jo on x86 or the carry-flag variants), producing branch-predictable, exception-free code that slots cleanly into hot loops without touching the exception machinery or sacrificing throughput.
What Is Arithmetic overflow detection with __builtin_add_overflow / std::add_overflow (and the upcoming contracts alternative)?
Signed integer overflow in C++ is undefined behavior — the compiler is legally allowed to assume it never happens, which means optimizers can and do eliminate overflow checks written naively with if (a + b < a). This isn’t a theoretical concern; GCC and Clang routinely delete such guards under -O2. The problem demands a solution that is both correct and efficient.
GCC and Clang expose __builtin_add_overflow(a, b, &result), along with __builtin_sub_overflow and __builtin_mul_overflow. These builtins perform the arithmetic in the mathematical integers, store the wrapped result in *result, and return true if the true value doesn’t fit in the result type. Crucially, the type of result drives the overflow semantics — mixing signed and unsigned types works predictably because the check is against the destination type, not the operands. MSVC offers UIntAdd, IntAdd, etc. from <intsafe.h> for similar unsigned coverage, though without the same generality.
int a = INT_MAX, b = 1, result;
if (__builtin_add_overflow(a, b, &result)) {
// overflow detected; result holds the wrapped value
}
Under the hood, modern compilers lower these to a single add + jo/jno (overflow flag check) on x86, or adds + branch on ARM — one instruction overhead, no undefined behavior.
C++26 is expected to introduce std::add_overflow and friends in <numeric>, standardizing the API surface across implementations. Separately, the Contracts proposal ([[pre]], [[post]]) enables expressing overflow preconditions declaratively, though contracts terminate rather than branch, making them unsuitable for recoverable overflow handling.
Common pitfalls: assuming the builtin is only for int — it works on any integral type including size_t. Forgetting that the result pointer type governs overflow semantics leads to subtle bugs when mixing widths. Finally, don’t use these builtins on floating-point; they’re strictly integral.
Practical Use Case in Finance
A high-frequency trading order aggregation engine must sum large 64-bit notional values across thousands of fills per second. Silent integer overflow here means a corrupted position — a catastrophic risk event.
Setup: Each fill carries a notional (quantity × price in cents). We accumulate these into a running total_notional. With values potentially in the billions, overflow is a real threat that must be caught immediately, not discovered during end-of-day reconciliation.
#include <cstdint>
#include <stdexcept>
#include <iostream>
#include <vector>
// Represents a single trade fill
struct Fill {
int64_t notional_cents; // qty * price in cents (can be large)
};
// Accumulates notional with overflow protection.
// Uses GCC/Clang __builtin_add_overflow; on MSVC use safeint or manual check.
int64_t aggregate_notional(const std::vector<Fill>& fills) {
int64_t total = 0;
for (const auto& fill : fills) {
int64_t next = 0;
// __builtin_add_overflow returns true if overflow would occur,
// storing the wrapped result in `next` (which we discard on error).
if (__builtin_add_overflow(total, fill.notional_cents, &next)) {
throw std::overflow_error(
"Notional accumulation overflowed int64 — "
"halt aggregation, alert risk desk immediately."
);
}
total = next;
}
return total;
}
int main() {
// Simulate fills approaching int64 limits
int64_t near_max = INT64_MAX - 1000;
std::vector<Fill> fills = {
{near_max},
{500}, // fine
{600}, // this tips over the edge
};
try {
int64_t result = aggregate_notional(fills);
std::cout << "Total notional: " << result << " cents\n";
} catch (const std::overflow_error& e) {
std::cerr << "[RISK ALERT] " << e.what() << '\n';
// In production: publish alert, reject batch, trigger circuit breaker
}
}
What this demonstrates: __builtin_add_overflow performs the addition and overflow detection in a single CPU instruction (ADD + JO on x86), with zero overhead on the happy path — critical for a hot loop. Compared to pre-checking with INT64_MAX - a < b, it is both safer and faster. The upcoming C++26 Contracts feature ([[pre: ...]]) will allow expressing these invariants declaratively at function boundaries, but __builtin_add_overflow remains the practical tool today for inline arithmetic guards in latency-sensitive paths.
Learn More: A Video Worth Watching
Understanding integer overflow vulnerabilities is crucial for developers working in quantitative finance, where precision and correctness directly impact trading systems and risk calculations. This video from Marcus Hutchins provides an accessible introduction to how binary integers work and the mechanics behind overflow conditions—foundational knowledge that contextualizes why C++ provides built-in overflow detection tools like __builtin_add_overflow and the standardized std::add_overflow (coming in C++26).
For quant developers, grasping these fundamentals clarifies why relying on manual bounds checking is error-prone compared to language-level solutions. The video breaks down overflow vulnerabilities in clear terms, helping you appreciate why modern C++ contracts and overflow detection mechanisms matter for building robust financial algorithms. If you want to strengthen your understanding of the security and correctness issues that these C++ features address, this is an excellent primer.
Conclusion
Detecting arithmetic overflow is no longer optional in production systems. With __builtin_add_overflow and its standard library counterpart std::add_overflow, C++ developers have efficient, portable tools to catch silent integer wraparound before it corrupts data or enables exploits.
The key takeaway is simple: overflow checks need not be expensive. Modern compilers translate these intrinsics into single CPU instructions on most platforms, making defensive arithmetic genuinely zero-cost. Whether you’re managing financial calculations, sizing buffers, or computing timestamps, a three-line safety check pays dividends.
C++26’s contracts proposal will eventually offer syntactic elegance, but don’t wait—start using overflow detection functions today. Experiment in your codebase, measure the performance impact (spoiler: it’s negligible), and establish overflow-safe patterns as standard practice.
In high-performance and financial systems, silent integer overflow is a liability masquerading as efficiency. Reclaim both safety and speed.
Want to Go Deeper?
- Explore more C++ feature articles: C++ for Quants — Features.